
How Spinify
Handles Security
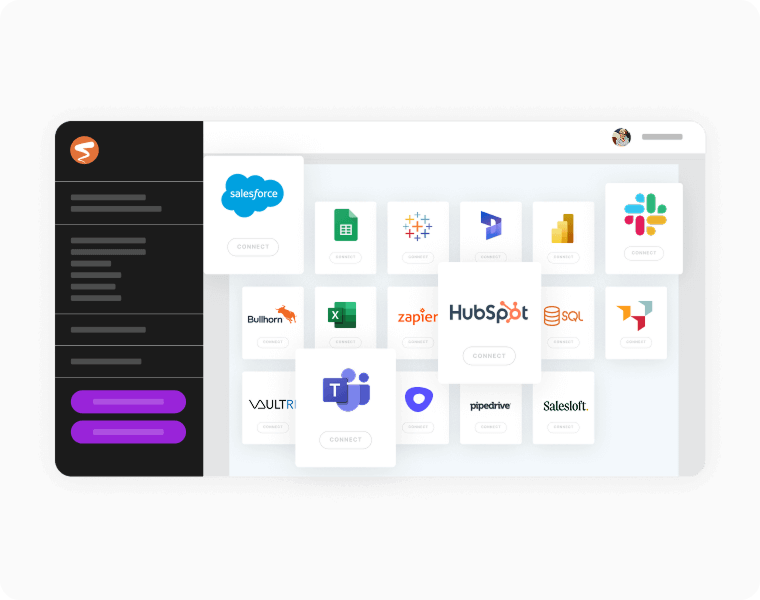
Integrated data apps mean you just need to confirm access. Spinify then handles all the syncing, and the leaderboards can be up and running in minutes.
How We Protect Your Data
Protecting customer data is core to everything we do at Spinify. We design our platform, infrastructure, and internal processes with privacy and security in mind, from the ground up.
We know that trust is earned, not assumed. That’s why we’re committed to continuously strengthening our security posture through independent audits, industry-leading encryption, and robust internal controls. As our platform evolves, so does our dedication to safeguarding your data.
Security at Spinify isn’t a feature, it’s a foundation.
We know that trust is earned, not assumed. That’s why we’re committed to continuously strengthening our security posture through independent audits, industry-leading encryption, and robust internal controls. As our platform evolves, so does our dedication to safeguarding your data.
Security at Spinify isn’t a feature, it’s a foundation.
SOC 2 Type 2 Compliance
Spinify is proudly SOC 2 Type 2 compliant (also referred to as SOC 2 Type II), affirming our commitment to the highest standards of data security and operational excellence.
SOC 2 Type 2 is a leading security framework designed specifically for modern SaaS businesses that manage sensitive customer information in the cloud. It is governed by the American Institute of Certified Public Accountants (AICPA) and evaluates how organizations implement and operate controls related to security, availability, confidentiality, and privacy.
What SOC 2 Type 2 Means for You
Unlike point-in-time certifications, SOC 2 Type 2 requires independent auditors to assess
how effectively security controls are implemented over a defined period, not just whether policies exist, but whether
they are actively followed and maintained.
Spinify’s compliance with SOC 2 Type 2 assures customers that:
how effectively security controls are implemented over a defined period, not just whether policies exist, but whether
they are actively followed and maintained.
Spinify’s compliance with SOC 2 Type 2 assures customers that:
Our security controls are tested in practice, not just documented.
We continuously monitor and enforce secure processes across our platform.
We follow strict access, encryption, and data governance standards, verified by external auditors.
This certification demonstrates that our systems and internal processes have passed rigorous, real-world scrutiny,
giving your team the confidence to trust Spinify with your most critical data.
Scope of Our SOC 2 Type 2 Certification
Our audit covers key operational and technical domains, including:
Your Data, Your Control
Spinify integrates with your systems to collect rep activity and performance data, helping you drive engagement, recognition, and results. The data required depends on your selected integrations and KPIs, and is intentionally minimal. End-user personal data is not required to use Spinify.
Your organization controls exactly what data is shared with Spinify, and access can be updated or removed at any time.
Your organization controls exactly what data is shared with Spinify, and access can be updated or removed at any time.
Platform Security by Design
We follow secure-by-design principles and implement rigorous safeguards to protect your data throughout its lifecycle:
Data in Transit:
Encrypted using TLS (SSL certificates issued by GoDaddy).
Data at Rest:
Zero Removable Media:
Access Controls:
Proactive Threat Protection
We take a proactive approach to platform security:
Infrastructure & Hosting
Spinify is a SaaS platform that is 100% cloud-based and hosted in AWS in the USA. We do not manage or operate any physical servers. Our infrastructure includes:
For more information, see Amazon’s Security & Compliance Center.
Application Security & Reliability
Security is built into every stage of our software development lifecycle:
Contact
If you have any questions about Spinify’s security practices, compliance standards, or require
additional documentation, our team is here to help.
additional documentation, our team is here to help.


